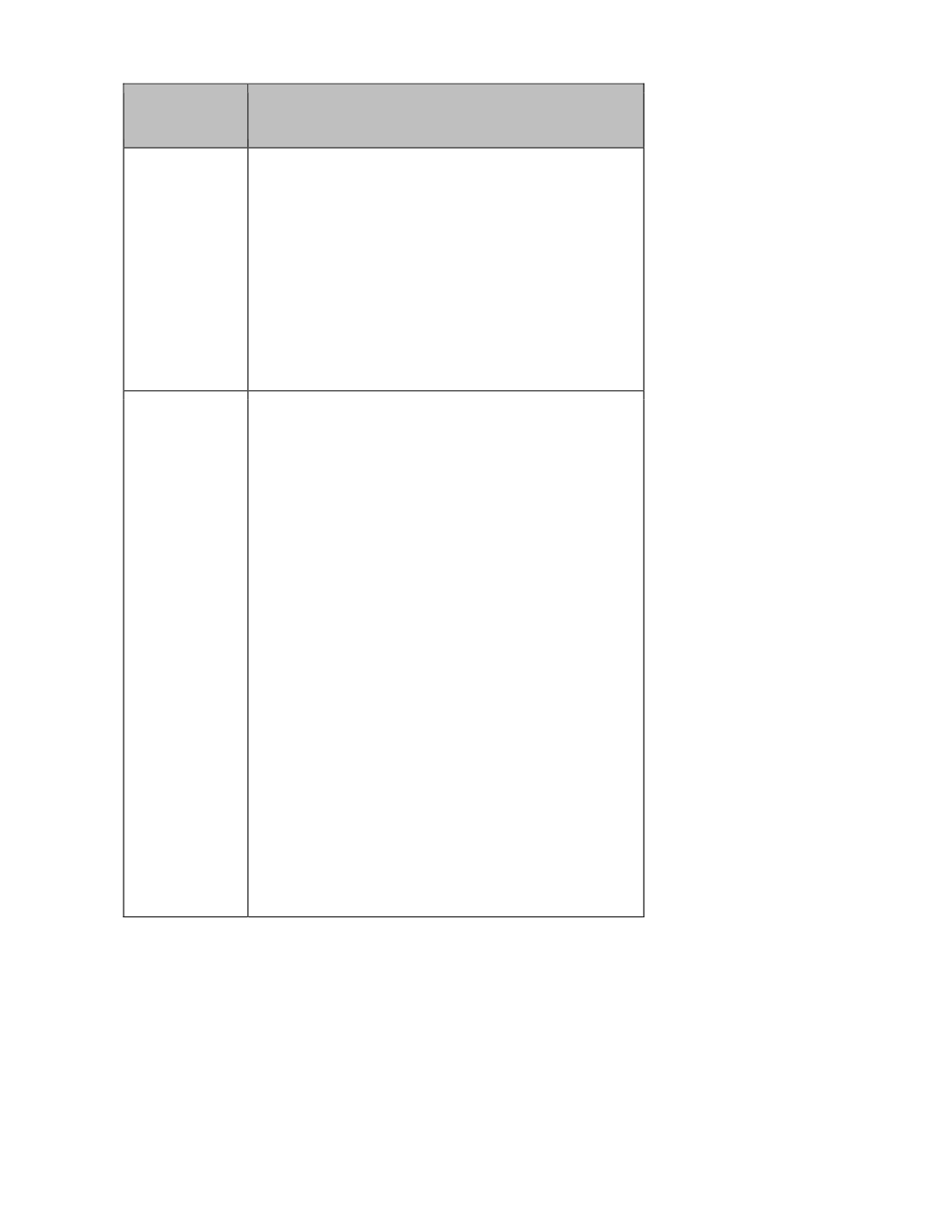
Situation
Appropriate Steps
Use of
portable
electronic
storage
devices
(“PSD”)
• carry out risk assessments to determine an
organisation’s real need in using PSDs
• develop policies on the use, distribution and
disposal of PSDs
• limit and control the circumstances of
downloading specific types and amount of
personal data to certain types of PSDs under
specific conditions by predefined users
• apply proper access controls (both logical and
physical) and/or encryption to protect personal
data in PSDs when applicable
Bring your
own device
(“BYOD”)
• carry out risk assessments to determine an
organisation’s real need in BYOD and its
technical capability to manage it
• develop BYOD policy to cover the following
specific areas:
– roles, responsibility and obligation of
organisations and individual users
– what criteria organisations would use to
allow personal data to be accessible
by/held in BYOD equipment
– security measures to protect personal data
collected and held by the organisation that
is being accessed/held by BYOD
equipment
– ways in which the personal data privacy of
the BYOD owners (and those who use the
BYOD equipment for personal use) may be
respected
• extend organisational retention, secondary
use, security and data access/correction
policies to cover personal data held in BYOD
equipment where appropriate
• periodically review and assess BYOD policy to
keep up with technological development and
business practice









