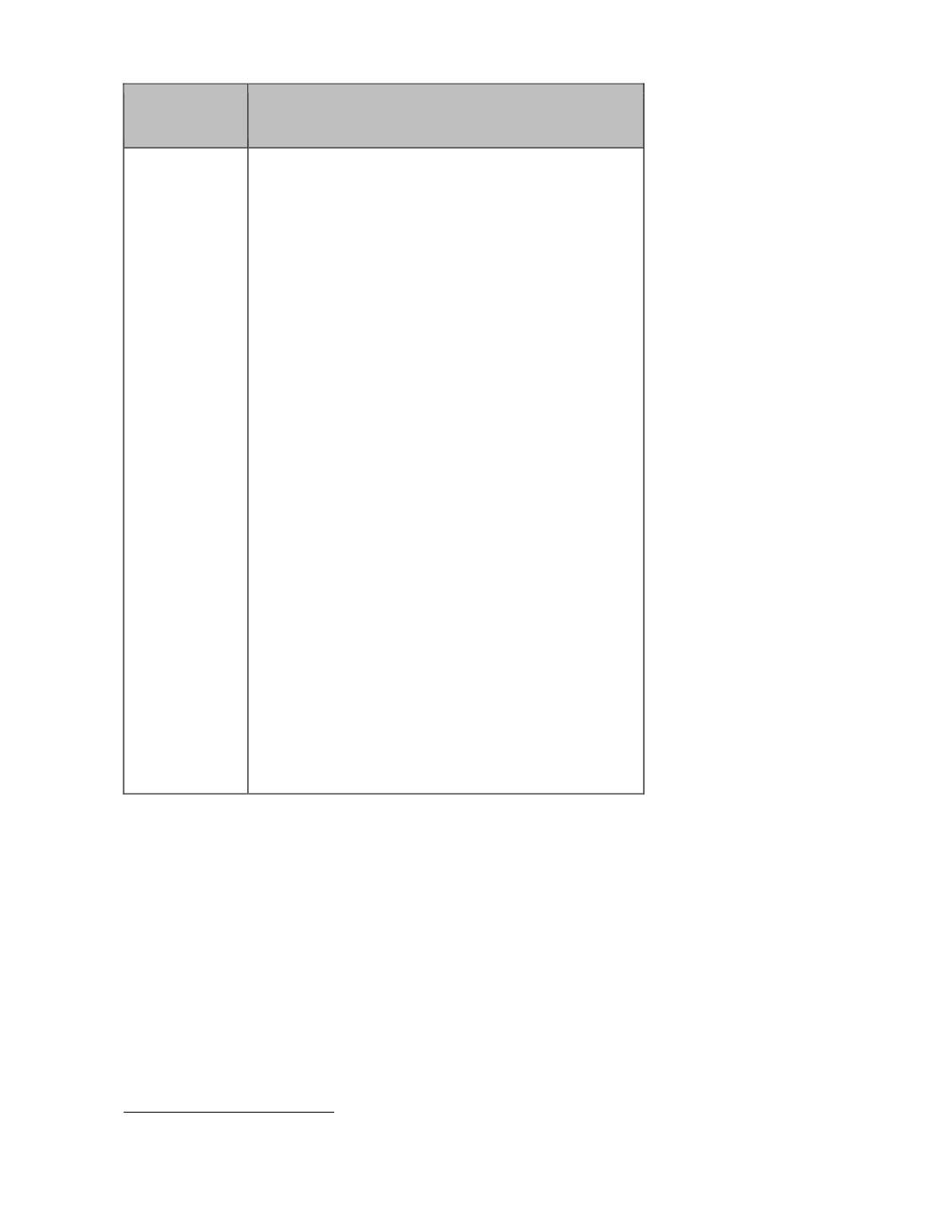
Situation
Appropriate Steps
IT operations
• develop operational policies, guidelines and
procedures to protect personal data stored
electronically to ensure confidentiality and
integrity of the data and accountability of
those who handle it, including (where
applicable):
– user access rights approval, management,
assignment and removal procedures
– password complexity, retry, reset and expiry
guidelines to prevent passwords from being
compromised
– change control approval and management
– segregation of production, testing and
development environments policy
– IT asset disposal and erasure standards to
ensure no leakage of personal data
– portable storage device use and protection
– anti-malware strategy and execution
– security patch and vulnerability
management for software, computers and
servers
– end-point security and data loss prevention
policies
– wired and wireless network security and
access control standards
– logging and monitoring of systems, user and
IT access procedures
– data centre and equipment physical
protection guidelines
– backup strategy and protection policy
2
2
If the file can be accessed through a URL, then even when there are no hyperlinks to the file, it can be searched and
“published” by search engines.









