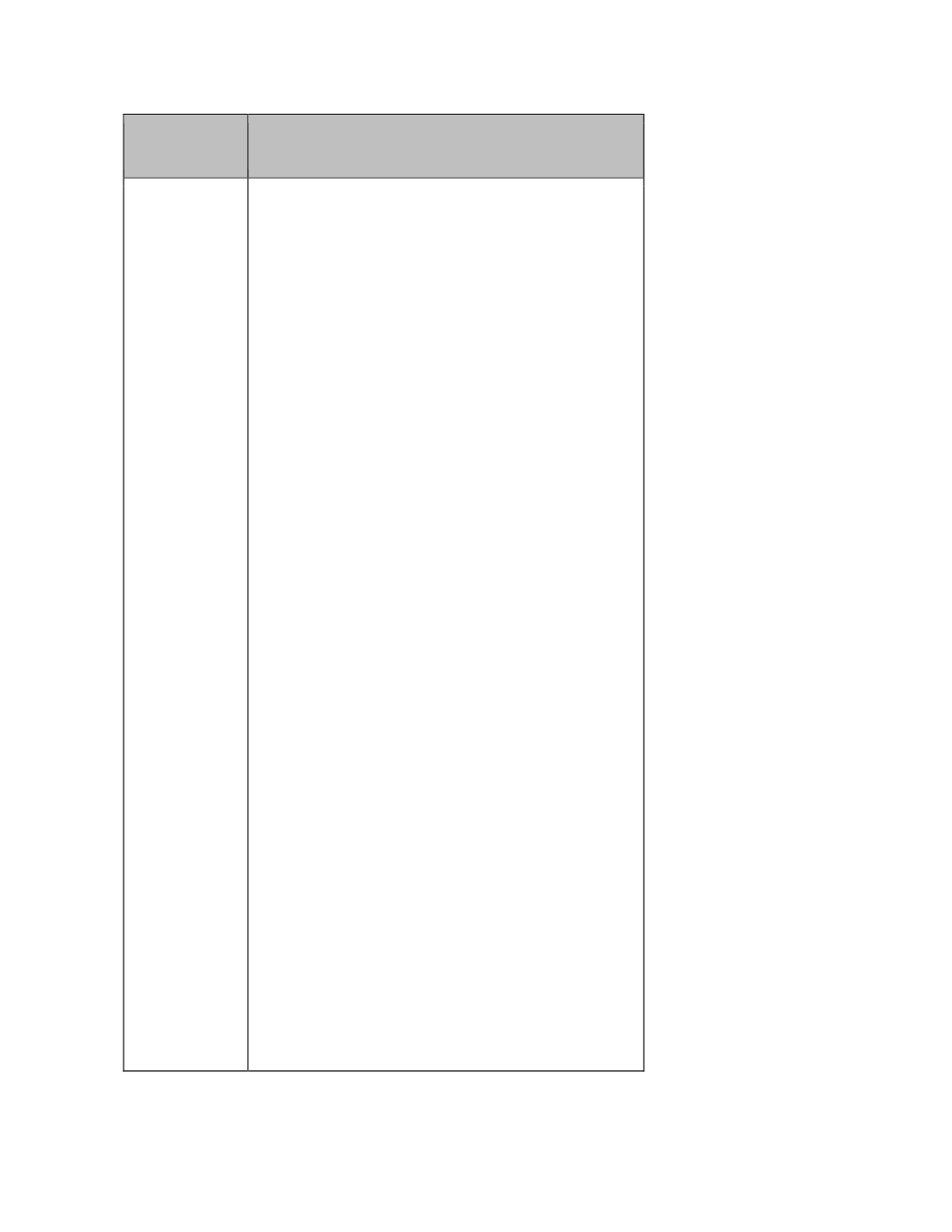
Suggested security measures when handling personal data by using various technologies:
Situation
Appropriate Steps
Websites
• scan websites for common vulnerability before
launch and thereafter at regular intervals
• develop controls to prevent files containing
personal data from being inadvertently stored
on websites, even when they are not referred
to by any hyperlinks
• use adequate encryption and access control
to avoid unauthorised interception, access or
alteration
• anonymise personal data displayed whenever
possible
• deploy adequate account protection:
– develop proper controls over password
complexity, retries, reset and periodic
change to prevent passwords from being
compromised
– avoid the use of “obvious” default account
names or passwords, such as data user’s
HKID number, date of birth or telephone
number
– consider deploying two-factor
authentication where the sensitivity of the
personal data warrants a high degree of
account protection
• adopt, where applicable, the following
additional technical safeguards:
– install and configure properly firewall and/or
intrusion detection/prevention systems to
guard against intrusion
– utilise three-tier architecture to isolate
database servers from becoming directly
accessible from the internet
– conduct regular vulnerability or penetration
assessments
– never use easily predictable methods (such
as using sequential or receipt numbers) in
hyperlinks to retrieve personal data, so as to
avoid unauthorised access by those who
would guess the hyperlinks
– disallow the storing of files containing
personal data in webservers without
adequate access control or encryption
protection









