Media Statements
Privacy Commissioner’s Office Publishes Two Investigation Reports on the Data Breach Incidents of (1) Kwong’s Art Jewellery Trading Company Limited and My Jewelry Management Limited and (2) Adastria Asia Co., Limited
Date: 21 Aug 2025
Privacy Commissioner’s Office Publishes Two Investigation Reports on the Data Breach Incidents of (1) Kwong’s Art Jewellery Trading Company Limited and My Jewelry Management Limited and (2) Adastria Asia Co., Limited
Upon completion of the investigations into the data breach incidents involving Kwong’s Art Jewellery Trading Company Limited (Kwong’s Art Jewellery) and My Jewelry Management Limited (My Jewelry), as well as Adastria Asia Co., Limited (Adastria), the Office of the Privacy Commissioner for Personal Data (PCPD) published the investigation reports today.
(1) Data Breach Incident of Kwong’s Art Jewellery and My Jewelry
The investigation arose from a data breach notification submitted by Kwong’s Art Jewellery and My Jewelry to the PCPD on 11 November 2024, reporting abnormalities in their shared information systems and receipt of messages from a threat actor which claimed that the data stored in the information systems of Kwong’s Art Jewellery and My Jewelry had been stolen. Upon inspection, Kwong’s Art Jewellery and My Jewelry confirmed that the data stored in their database server had been stolen and deleted (Incident).
Kwong’s Art Jewellery is the parent company of My Jewelry and is engaged in jewellery manufacturing and wholesale, while My Jewelry is a jewellery retail company which operates the brand “My Jewelry”. Kwong’s Art Jewellery and My Jewelry have been jointly managing and using the affected information systems, including the servers, applications and databases.
The investigation revealed that the threat actor conducted a brute-force attack to obtain the credentials of an administrator account (Account). The threat actor utilised the Account to gain access to the information systems of the two companies and performed lateral movement within the network, which included implanting a Trojan Horse program on a desktop computer used for internal system development and programming. This allowed the threat actor to obtain the source code to control the database server, which led to the successful exfiltration and deletion of the personal data stored therein.
According to the information provided by Kwong’s Art Jewellery and My Jewelry, approximately 79,400 data subjects were affected by the Incident, including corporate customers and current and former employees of Kwong’s Art Jewellery, as well as retail customers and current and former employees of My Jewelry. The personal data affected included the names, Hong Kong Identity Card numbers, dates of birth, telephone numbers, addresses and commencement dates of employment of employees, as well as the names, Hong Kong Identity Card numbers (first four alphanumeric characters), years and months of birth, telephone numbers, email addresses, and membership numbers of customers.
Following the Incident, Kwong’s Art Jewellery and My Jewelry implemented various improvement measures to enhance the security of their information systems, which included resetting login passwords for all users, updating operating systems of servers, antivirus software and firewall, as well as deploying “extended detection and response” tools for continuous monitoring of their information systems, etc. In addition, Kwong’s Art Jewellery and My Jewelry notified all affected data subjects after the Incident.
The PCPD conducted seven rounds of inquiries and reviewed the information provided by Kwong’s Art Jewellery and My Jewelry in relation to the Incident, and the follow-up and remedial actions taken by the two companies after the Incident. Having considered the circumstances of the Incident and the information obtained during the investigation, the Privacy Commissioner for Personal Data (Privacy Commissioner), Ms Ada CHUNG Lai-ling, found that the following deficiencies of Kwong’s Art Jewellery and My Jewelry contributed to the occurrence of the Incident (See Annex 1 for details):-
Based on the above, the Privacy Commissioner found that Kwong’s Art Jewellery and My Jewelry had not taken all practicable steps to ensure that the personal data involved was protected against unauthorised or accidental access, processing, erasure, loss or use, thereby contravening Data Protection Principle (DPP) 4(1) of the Personal Data (Privacy) Ordinance (PDPO) concerning the security of personal data.
The Privacy Commissioner has served Enforcement Notices on Kwong’s Art Jewellery and My Jewelry, directing them to take measures to remedy the contraventions and prevent recurrence of similar contraventions in future.
(2) Data Breach Incident of Adastria
The investigation arose from a data breach notification submitted by Adastria to the PCPD on 18 November 2024, reporting that its customer relationship management platform and e-commerce platform (collectively, the Affected Platforms) were accessed by an unauthorised third party, which resulted in the exfiltration of the personal data of Adastria’s customers (Adastria Incident).
The investigation revealed that the Affected Platforms operated as a Software-as-a-Service (SaaS) which was provided by a third-party vendor (the Platform Vendor). In the Adastria Incident, the threat actor used the credentials of an administrator account of a current employee to connect to the Affected Platforms from an unknown overseas IP address and downloaded the order information stored therein.
Adastria is a Japanese multinational corporation engaging in fashion retail in various Asian countries. At the time of the Adastria Incident, Adastria was managing the sales of its affiliated brands (including GLOBAL WORK, “niko and …”, LOWRYS FARM, Heather, JEANASiS, studio CLIP, repipi armario, LEPSIM, PAGEBOY) in Hong Kong through its online platform “dot st HK”. The personal data of a total of 59,205 customers was affected by the Adastria Incident. The personal data affected included the names, telephone numbers and order information of customers (including the transaction reference numbers, order dates, membership numbers, delivery methods, deliver/pickup dates, delivery addresses, product names and descriptions, and price information).
During the course of investigation, Adastria discovered that the affected personal data was disclosed in the Dark Web approximately two months after the Adastria Incident and was made available for download.
Adastria notified all affected customers after the Adastria Incident. Adastria also implemented various remedial measures to address the deficiencies identified in the Adastria Incident, including enabling the security functions of the Affected Platforms, such as password measures, multi-factor authentication and IP address restriction function, and deploying an endpoint detection and response solution to detect and block any malicious activities on its information systems.
The PCPD conducted five rounds of inquiries and reviewed the information provided by Adastria in relation to the Adastria Incident, including two investigation reports provided by a third-party consultant engaged by Adastria, and the follow-up and remedial actions taken by Adastria after the Adastria Incident. Having considered the circumstances of the Adastria Incident and the information obtained during the investigation, the Privacy Commissioner found that the following deficiencies of Adastria contributed to the occurrence of the Adastria Incident (see Annex 2 for details):-
Based on the above, the Privacy Commissioner found that Adastria had not taken all practicable steps to ensure that the personal data involved was protected against unauthorised or accidental access, processing, erasure, loss or use, thereby contravening DPP4(1) of the PDPO concerning the security of personal data.
The Privacy Commissioner has served an Enforcement Notice on Adastria, directing it to take measures to remedy the contravention and prevent recurrence of similar contraventions in the future.
The Privacy Commissioner notes that both data breach incidents involved retail organisations which held significant amounts of customers’ personal data, with evidence suggesting subsequent disclosure of customers’ data in the Dark Web in one incident. These incidents demonstrate the link between data breach incidents and both the illicit sale of personal data for profit, as well as the use of personal data by fraudsters in different fraudulent activities. The Privacy Commissioner recognises that retail organisations in general may have limited resources for cybersecurity. However, given the rapidly evolving cybersecurity risks and the increasing trend of using personal data in fraudulent activities in recent years, the Privacy Commissioner, Ms Ada CHUNG Lai-ling, reminds the retail industry and organisations that hold significant amounts of personal data of customers, “In the face of escalating cybersecurity threats, organisations should recognise that the personal data in their possession are valuable assets and allocate sufficient resources on cybersecurity and data security in order to safeguard the personal data in their possession, thereby complying with the requirements of the PDPO and meeting the reasonable expectations of data subjects.”
The Privacy Commissioner recommends organisations to adopt appropriate organisational and technical measures to safeguard their information systems that contain personal data. In particular, organisations should:


(1) Data Breach Incident of Kwong’s Art Jewellery and My Jewelry
The investigation arose from a data breach notification submitted by Kwong’s Art Jewellery and My Jewelry to the PCPD on 11 November 2024, reporting abnormalities in their shared information systems and receipt of messages from a threat actor which claimed that the data stored in the information systems of Kwong’s Art Jewellery and My Jewelry had been stolen. Upon inspection, Kwong’s Art Jewellery and My Jewelry confirmed that the data stored in their database server had been stolen and deleted (Incident).
Kwong’s Art Jewellery is the parent company of My Jewelry and is engaged in jewellery manufacturing and wholesale, while My Jewelry is a jewellery retail company which operates the brand “My Jewelry”. Kwong’s Art Jewellery and My Jewelry have been jointly managing and using the affected information systems, including the servers, applications and databases.
The investigation revealed that the threat actor conducted a brute-force attack to obtain the credentials of an administrator account (Account). The threat actor utilised the Account to gain access to the information systems of the two companies and performed lateral movement within the network, which included implanting a Trojan Horse program on a desktop computer used for internal system development and programming. This allowed the threat actor to obtain the source code to control the database server, which led to the successful exfiltration and deletion of the personal data stored therein.
According to the information provided by Kwong’s Art Jewellery and My Jewelry, approximately 79,400 data subjects were affected by the Incident, including corporate customers and current and former employees of Kwong’s Art Jewellery, as well as retail customers and current and former employees of My Jewelry. The personal data affected included the names, Hong Kong Identity Card numbers, dates of birth, telephone numbers, addresses and commencement dates of employment of employees, as well as the names, Hong Kong Identity Card numbers (first four alphanumeric characters), years and months of birth, telephone numbers, email addresses, and membership numbers of customers.
Following the Incident, Kwong’s Art Jewellery and My Jewelry implemented various improvement measures to enhance the security of their information systems, which included resetting login passwords for all users, updating operating systems of servers, antivirus software and firewall, as well as deploying “extended detection and response” tools for continuous monitoring of their information systems, etc. In addition, Kwong’s Art Jewellery and My Jewelry notified all affected data subjects after the Incident.
The PCPD conducted seven rounds of inquiries and reviewed the information provided by Kwong’s Art Jewellery and My Jewelry in relation to the Incident, and the follow-up and remedial actions taken by the two companies after the Incident. Having considered the circumstances of the Incident and the information obtained during the investigation, the Privacy Commissioner for Personal Data (Privacy Commissioner), Ms Ada CHUNG Lai-ling, found that the following deficiencies of Kwong’s Art Jewellery and My Jewelry contributed to the occurrence of the Incident (See Annex 1 for details):-
- Failure to delete a former employee’s account in a timely manner;
- Lack of effective security and detection measures in the information systems;
- Outdated operating systems of servers;
- Lack of policies and guidelines on information security; and
- Absence of security assessments and audits of the information systems.
Based on the above, the Privacy Commissioner found that Kwong’s Art Jewellery and My Jewelry had not taken all practicable steps to ensure that the personal data involved was protected against unauthorised or accidental access, processing, erasure, loss or use, thereby contravening Data Protection Principle (DPP) 4(1) of the Personal Data (Privacy) Ordinance (PDPO) concerning the security of personal data.
The Privacy Commissioner has served Enforcement Notices on Kwong’s Art Jewellery and My Jewelry, directing them to take measures to remedy the contraventions and prevent recurrence of similar contraventions in future.
(2) Data Breach Incident of Adastria
The investigation arose from a data breach notification submitted by Adastria to the PCPD on 18 November 2024, reporting that its customer relationship management platform and e-commerce platform (collectively, the Affected Platforms) were accessed by an unauthorised third party, which resulted in the exfiltration of the personal data of Adastria’s customers (Adastria Incident).
The investigation revealed that the Affected Platforms operated as a Software-as-a-Service (SaaS) which was provided by a third-party vendor (the Platform Vendor). In the Adastria Incident, the threat actor used the credentials of an administrator account of a current employee to connect to the Affected Platforms from an unknown overseas IP address and downloaded the order information stored therein.
Adastria is a Japanese multinational corporation engaging in fashion retail in various Asian countries. At the time of the Adastria Incident, Adastria was managing the sales of its affiliated brands (including GLOBAL WORK, “niko and …”, LOWRYS FARM, Heather, JEANASiS, studio CLIP, repipi armario, LEPSIM, PAGEBOY) in Hong Kong through its online platform “dot st HK”. The personal data of a total of 59,205 customers was affected by the Adastria Incident. The personal data affected included the names, telephone numbers and order information of customers (including the transaction reference numbers, order dates, membership numbers, delivery methods, deliver/pickup dates, delivery addresses, product names and descriptions, and price information).
During the course of investigation, Adastria discovered that the affected personal data was disclosed in the Dark Web approximately two months after the Adastria Incident and was made available for download.
Adastria notified all affected customers after the Adastria Incident. Adastria also implemented various remedial measures to address the deficiencies identified in the Adastria Incident, including enabling the security functions of the Affected Platforms, such as password measures, multi-factor authentication and IP address restriction function, and deploying an endpoint detection and response solution to detect and block any malicious activities on its information systems.
The PCPD conducted five rounds of inquiries and reviewed the information provided by Adastria in relation to the Adastria Incident, including two investigation reports provided by a third-party consultant engaged by Adastria, and the follow-up and remedial actions taken by Adastria after the Adastria Incident. Having considered the circumstances of the Adastria Incident and the information obtained during the investigation, the Privacy Commissioner found that the following deficiencies of Adastria contributed to the occurrence of the Adastria Incident (see Annex 2 for details):-
- Weak password management;
- Failure to enable multi-factor authentication for access to accounts;
- Lack of awareness to ensure the security of personal data; and
- Failure to conduct proper security reviews on the Affected Platforms.
Based on the above, the Privacy Commissioner found that Adastria had not taken all practicable steps to ensure that the personal data involved was protected against unauthorised or accidental access, processing, erasure, loss or use, thereby contravening DPP4(1) of the PDPO concerning the security of personal data.
The Privacy Commissioner has served an Enforcement Notice on Adastria, directing it to take measures to remedy the contravention and prevent recurrence of similar contraventions in the future.
The Privacy Commissioner notes that both data breach incidents involved retail organisations which held significant amounts of customers’ personal data, with evidence suggesting subsequent disclosure of customers’ data in the Dark Web in one incident. These incidents demonstrate the link between data breach incidents and both the illicit sale of personal data for profit, as well as the use of personal data by fraudsters in different fraudulent activities. The Privacy Commissioner recognises that retail organisations in general may have limited resources for cybersecurity. However, given the rapidly evolving cybersecurity risks and the increasing trend of using personal data in fraudulent activities in recent years, the Privacy Commissioner, Ms Ada CHUNG Lai-ling, reminds the retail industry and organisations that hold significant amounts of personal data of customers, “In the face of escalating cybersecurity threats, organisations should recognise that the personal data in their possession are valuable assets and allocate sufficient resources on cybersecurity and data security in order to safeguard the personal data in their possession, thereby complying with the requirements of the PDPO and meeting the reasonable expectations of data subjects.”
The Privacy Commissioner recommends organisations to adopt appropriate organisational and technical measures to safeguard their information systems that contain personal data. In particular, organisations should:
- Establish clear internal policies and procedures to safeguard the security of information systems and ensure thorough implementation of the same;
- Implement effective measures to prevent, detect and respond to cyberattacks, including conducting regular vulnerability scans and patching cybersecurity vulnerabilities in a timely manner;
- Cease the use of end-of-support software and upgrade software in a timely manner;
- Enhance password management of information systems and adopt multi-factor authentication;
- Conduct comprehensive security risk reviews and audits for information systems regularly;
- Configure appropriate security functions on service platforms provided by third-party vendors and conduct regular security review;
- Formulate a data breach response plan; and
- Provide appropriate training to employees to improve their data security awareness.

The Privacy Commissioner, Ms Ada CHUNG Lai-ling, published two investigation reports on data breach incidents.

The Privacy Commissioner, Ms Ada CHUNG Lai-ling, explained two investigation reports on data breach incidents.
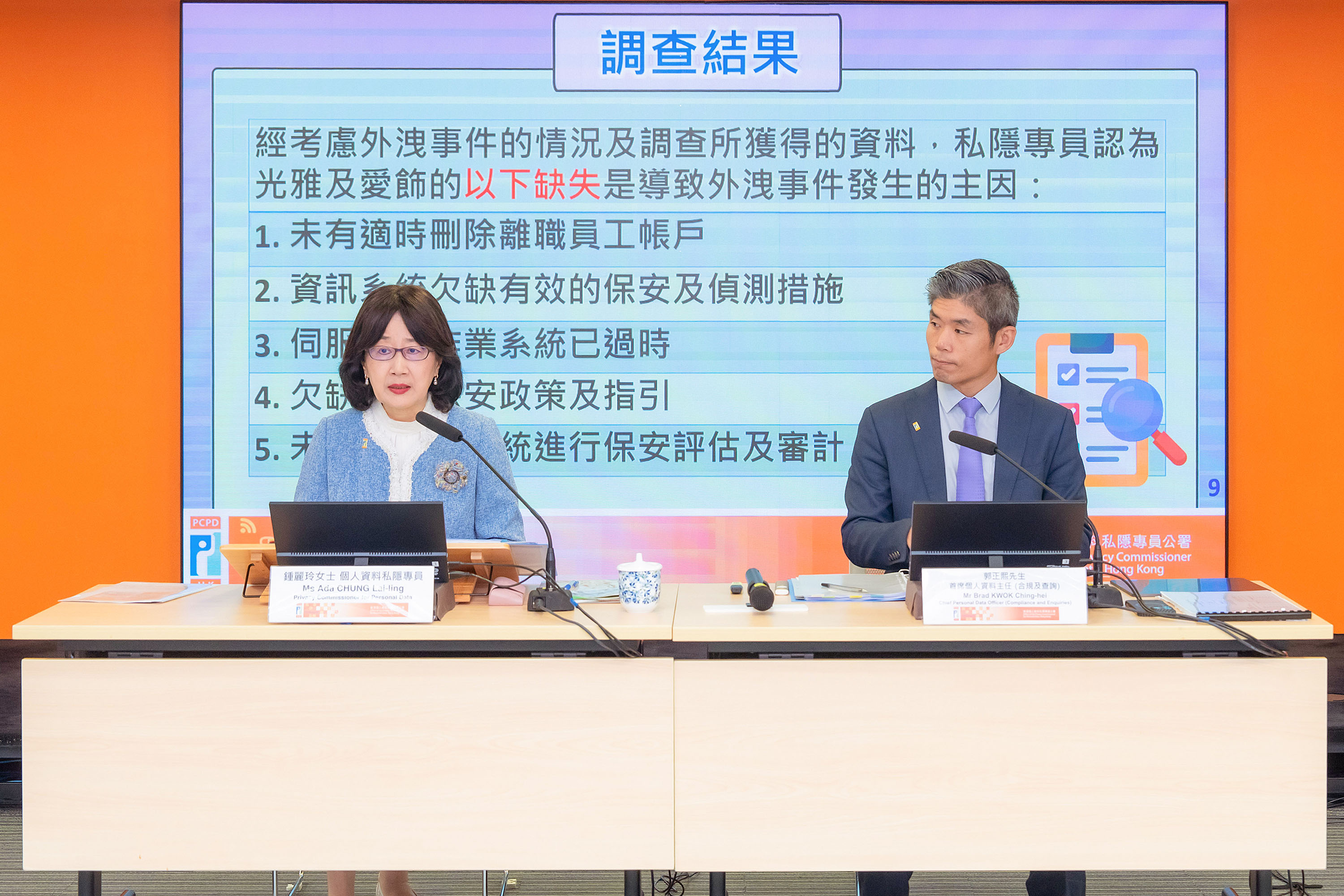
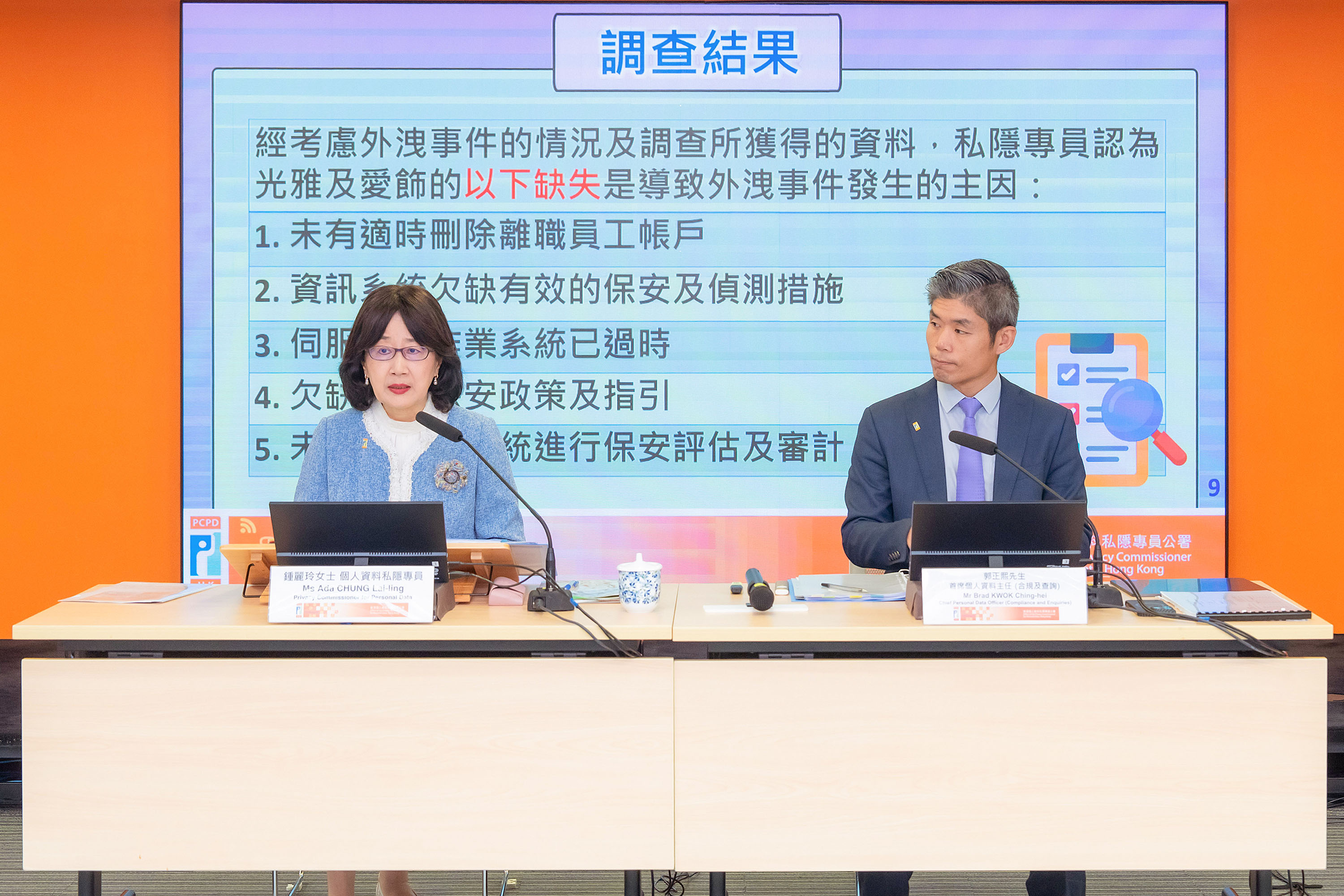
The Privacy Commissioner, Ms Ada CHUNG Lai-ling (left), and Chief Personal Data Officer (Compliance and Enquiries), Mr Brad KWOK Ching-hei (right), explained the two investigation reports of the data breach incidents.
[2] https://www.pcpd.org.hk/Toolkit/en/
Annex 1
Annex 1
Data Breach Incident of Kwong’s Art Jewellery Trading Company Limited
and My Jewelry Management Limited
Deficiencies that Contributed to the Incident
and My Jewelry Management Limited
Deficiencies that Contributed to the Incident
-
Failure to delete a former employee’s account in a timely manner: The Account was left idle for more than 13 years and the multi-factor authentication and account lockout function were not enabled for the Account at the time of the Incident. The threat actor eventually gained access to the information systems of Kwong’s Art Jewellery and My Jewelry via the Account and stole and deleted the personal data stored in the database server;
-
Lack of effective security and detection measures in the information systems: The firewall and antivirus software deployed by Kwong’s Art Jewellery and My Jewelry were outdated, which led to the failure to effectively defend against the cyberattack. Moreover, Kwong’s Art Jewellery and My Jewelry did not implement additional protective measures for effective real-time or regular monitoring of the activities within their information systems;
-
Outdated operating systems of servers: The operating system of the affected database server was not up-to-date and the vendor had discontinued support for the relevant operating system for four years. Kwong’s Art Jewellery and My Jewelry not only failed to update the operating system of the database server in a timely manner, but also failed to implement any additional security measures at the time of the Incident;
-
Lack of policies and guidelines on information security: Kwong’s Art Jewellery and My Jewelry did not establish written policies or guidelines on system security, account management, password requirements, activity monitoring, and system updates for staff members to follow. In addition, they failed to formulate response plans and reporting mechanisms for data security incidents; and
- Absence of security assessments and audits of the information systems: Kwong’s Art Jewellery and My Jewelry had not conducted any forms of security assessments and audits on their information systems to identify potential information security risks before the Incident.
Data Breach Incident of Adastria Asia Co., Limited
Deficiencies that Contributed to the Adastria Incident
Deficiencies that Contributed to the Adastria Incident
-
Weak password management: The passwords for all users of the Affected Platforms consisted of simple six-digit password combinations and had remained unchanged for two years before the Adastria Incident. Despite various password management measures applicable to the Affected Platforms were provided by the Platform Vendor, including setting the minimum length and complexity of password, auto-expiration of password, as well as the function of account lockout after repeated failed login attempts, Adastria did not configure these readily available password management measures;
-
Failure to enable multi-factor authentication (MFA) for access to accounts: While MFA was a readily available security function of the Affected Platforms offered by the Platform Vendor, Adastria did not enable MFA for all user accounts at the time of the Adastria Incident, including the administrator account that was compromised;
-
Lack of awareness to ensure the security of personal data: The Platform Vendor provided a range of security features for the Affected Platforms, including password management measures, MFA function, monitoring login function and IP address restriction function. However, Adastria did not enable any of these security measures at the time of the Adastria Incident; and
- Failure to conduct proper security reviews on the Affected Platforms: Although the Platform Vendor would conduct regular security reviews of the infrastructure of the Affected Platforms, Adastria failed to conduct any security reviews from the perspective of a service user before the Adastria Incident.